SatGate Agent Control Plane
Govern local AI agents before they touch expensive models, sensitive APIs, paid tools, or customer data. SatGate gives every agent bounded authority, visible spend, controlled delegation, and instant revocation.
Let agents work — without giving them blank checks, permanent keys, or invisible authority.
No permanent keys
Agents get temporary authority for the job, not reusable secrets that linger after the work is done.
Business limits built in
Each agent works inside the scope, budget, customer boundary, and expiration you set.
Delegation you can prove
When an agent hands work to another agent, SatGate shows who delegated what — and where the limits held.
Spend visible and stoppable
Every action is measured before cost gets out of hand, with revocation ready when risk changes.
Run autonomous agents with authority you can explain.
AI agents are starting to call APIs, use paid tools, delegate work, and act across customer environments. A production team needs more than connection and logs — it needs a way to decide what each agent is allowed to do before the action happens.
SatGate turns agent authority into a governed business object: scoped, budgeted, delegated, metered, audited, and revocable. The agent can move fast, but it never gets unlimited power.
Start with zero standing access
Agents do not wake up holding broad, reusable keys. They earn temporary authority for the job in front of them.
Give every agent a bounded mandate
Each capability carries the business limits that matter: scope, budget, tenant, expiry, delegation, and revocation.
Control delegated work
When an agent spins up a worker, SatGate keeps the worker narrower than the parent and proves the handoff later.
Stop spend before it happens
Budget checks run before model, API, SaaS, or MCP tool calls turn into real cost.
Show proof teams can trust
Security and finance get a clear record of who acted, what was allowed, what was denied, and what it cost.
Revoke without drama
Shut down an agent, worker, route, tenant, or budget without rotating every upstream provider secret.
From connected agents to governed agents.
Most agent stacks focus on getting tools connected. SatGate focuses on whether the agent should be allowed to act, spend, delegate, or continue — and proving that decision afterward.
Connection
Agents can reach models, APIs, and MCP tools.
Control
SatGate decides what authority, budget, and delegation each agent receives.
Proof
Every allowed, denied, charged, or revoked action leaves a clear audit trail.
Revenue
The same request path can charge robot customers when agent traffic becomes monetizable.
See exactly how agent authority moves.
When one agent delegates work to another, SatGate keeps the child narrower than the parent. Security teams can see the chain of authority, the budget attached to it, and where policy stopped the handoff.
Clear outcomes, not raw logs.
SatGate shows what happened in plain English: approved work, protected budget, revoked access, tenant isolation, and contained delegation.
Approved work
The agent completes authorized tasks through SatGate, with policy and tenant context attached.
Budget protected
Spend caps stop runaway loops before the next expensive call leaves the request path.
Access revoked
A kill switch cuts off a risky agent or delegated worker immediately.
Tenant isolated
Customer boundaries stay intact even when agents call shared tools or APIs.
Delegation contained
A worker can only receive the narrower authority the parent was allowed to hand off.
See the control loop end to end.
The walkthrough shows the control loop end to end: an agent receives bounded authority, delegates safely, hits real policy checks, leaves an audit trail, and can be shut down immediately.
A one-page view of the control model.
Use the proof card to explain the Agent Control Plane in a security review: no permanent keys, bounded authority, controlled delegation, visible spend, and instant revocation.
Download proof card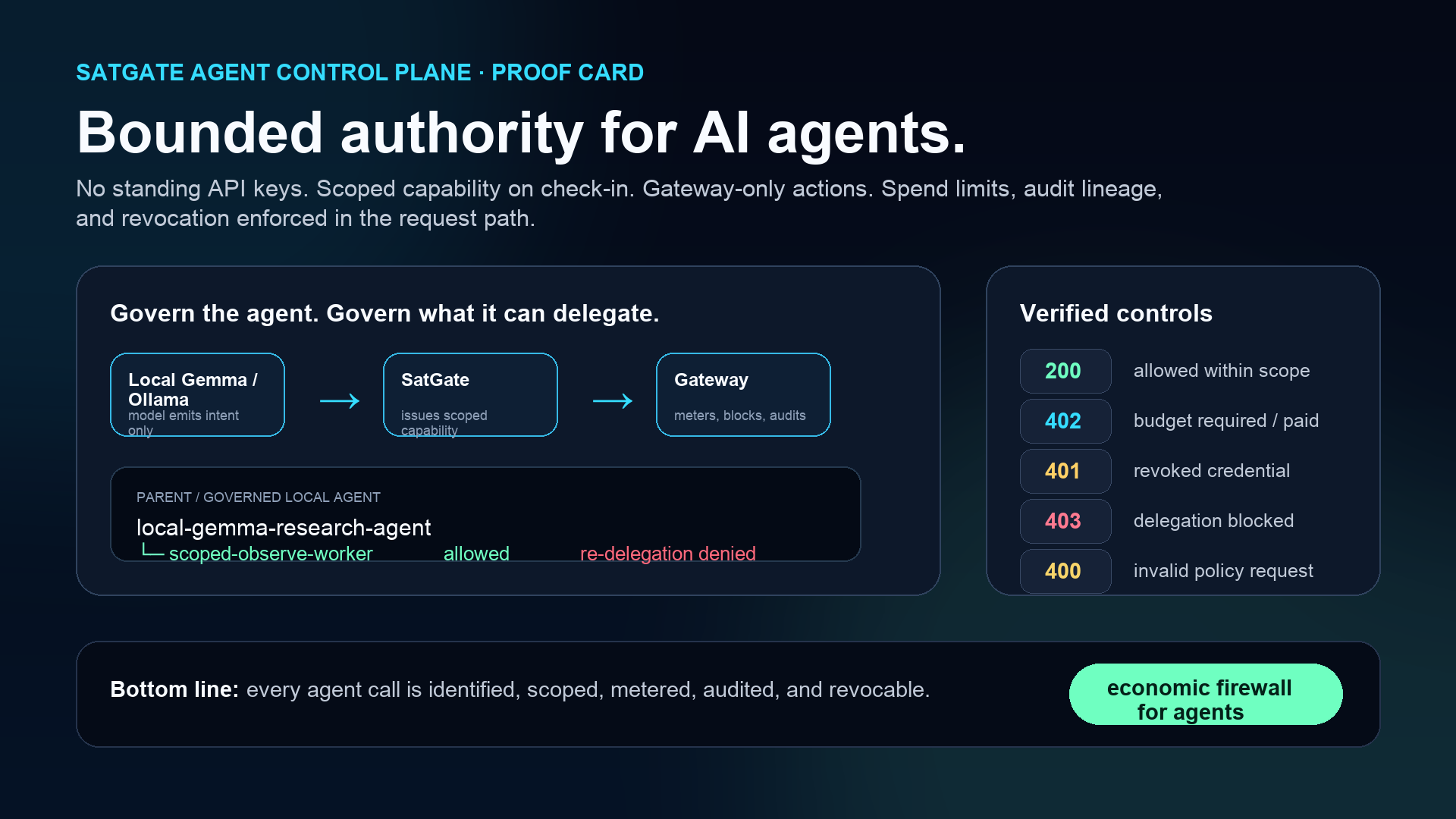
Agent control-plane FAQ
SatGate is for teams that want autonomous agents in production without handing them permanent keys, unmanaged delegation, or uncontrolled spend.
What is an agent control plane?
An agent control plane gives teams a live way to govern AI agents: what they can access, how much they can spend, what they can delegate, and when their authority should end. SatGate puts that control in the path of each agent action.
How is an agent control plane different from an API gateway?
An API gateway protects services. An agent control plane governs the agents using those services: their budget, customer boundary, delegation rights, audit trail, and ability to be revoked instantly.
Why do local AI agents need no standing authority?
Standing API keys give an agent reusable power even after the task, budget, tenant, or policy context changes. SatGate keeps local agents untrusted by default; they check in, receive short-lived scoped authority, and lose that authority when policy, budget, expiry, or revocation says stop.
How does SatGate control agent delegation?
SatGate lets a parent agent hand off only the authority it is allowed to share. The worker gets narrower limits, the handoff is visible, and attempts to exceed policy are blocked before they become spend or risk.
Related economic control-plane topics
Economic firewall
The request-path enforcement layer for agent access, spend, and Charge.
Agent API governance
Replace broad API keys with policy-bound, auditable agent authority.
Agent capability tokens
Encode route, budget, expiry, delegation, and revocation into agent access.
Revocable agent credentials
Kill agent access without rotating every upstream provider secret.
MCP governance
Apply budget, revocation, and audit controls to agent tool calls.
SatGate for Hermes Agent
Govern local Hermes/Open WebUI agent workflows with SatGate in the request path.
Turn local agents into governed enterprise actors.
No standing API keys. No unmanaged delegation. No invisible spend.
Book a demo